The following guide describes the required steps to configure sklera with Active Directory so your users can access the sklera CMS with their AD credentials.
Active Directory is available in the hosting variants On Premise and Private Cloud. We support the use of Entra ID/Azure AD, ADFS 3.0 or ADFS 4.0
Microsoft Entra ID (former Azure AD)
To connect to your Entra ID/ Azure AD it is required to register sklera as a new company app within Azure. Please use the following settings:
Redirect URLS: - https://SERVER_URL/_oauth/azureAd - https://SERVER_URL/_oauth/azureAd?close
Subsequently kindly securely submit the following information to sklera GmbH <support@sklera.tv>:
- Application (client) ID
- Directory (tenant) ID
- Client secret (value)
Configure Microsoft Entra ID for sklera
Open Microsoft Entra ID:
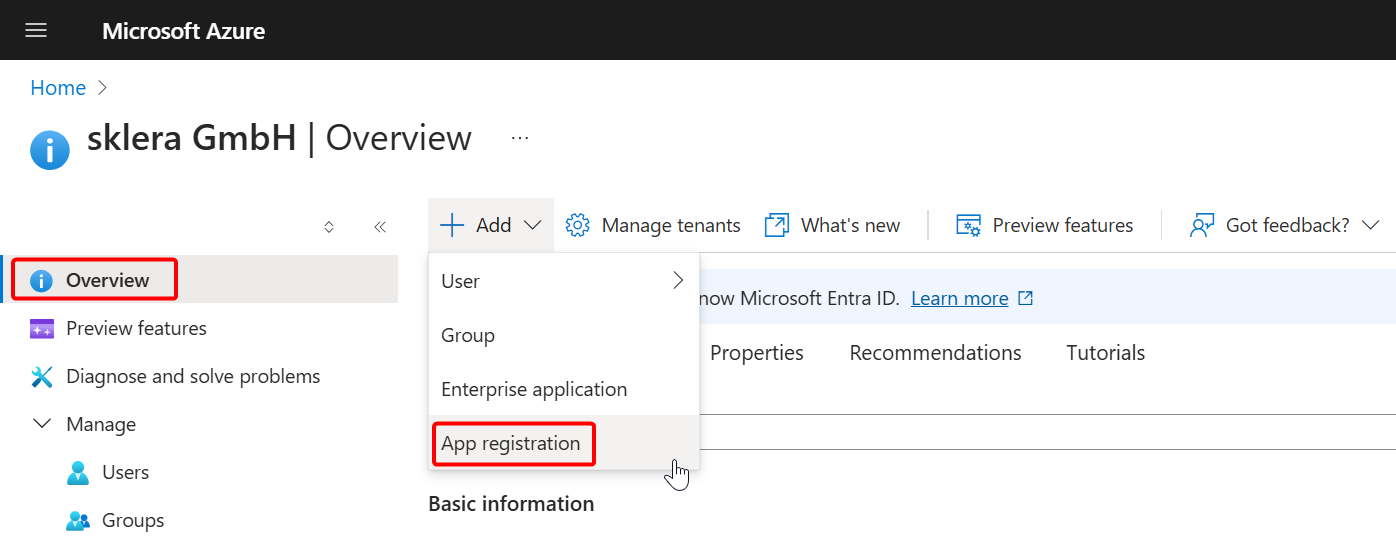
Select App registration:

Configure branding:

Configure Authentication: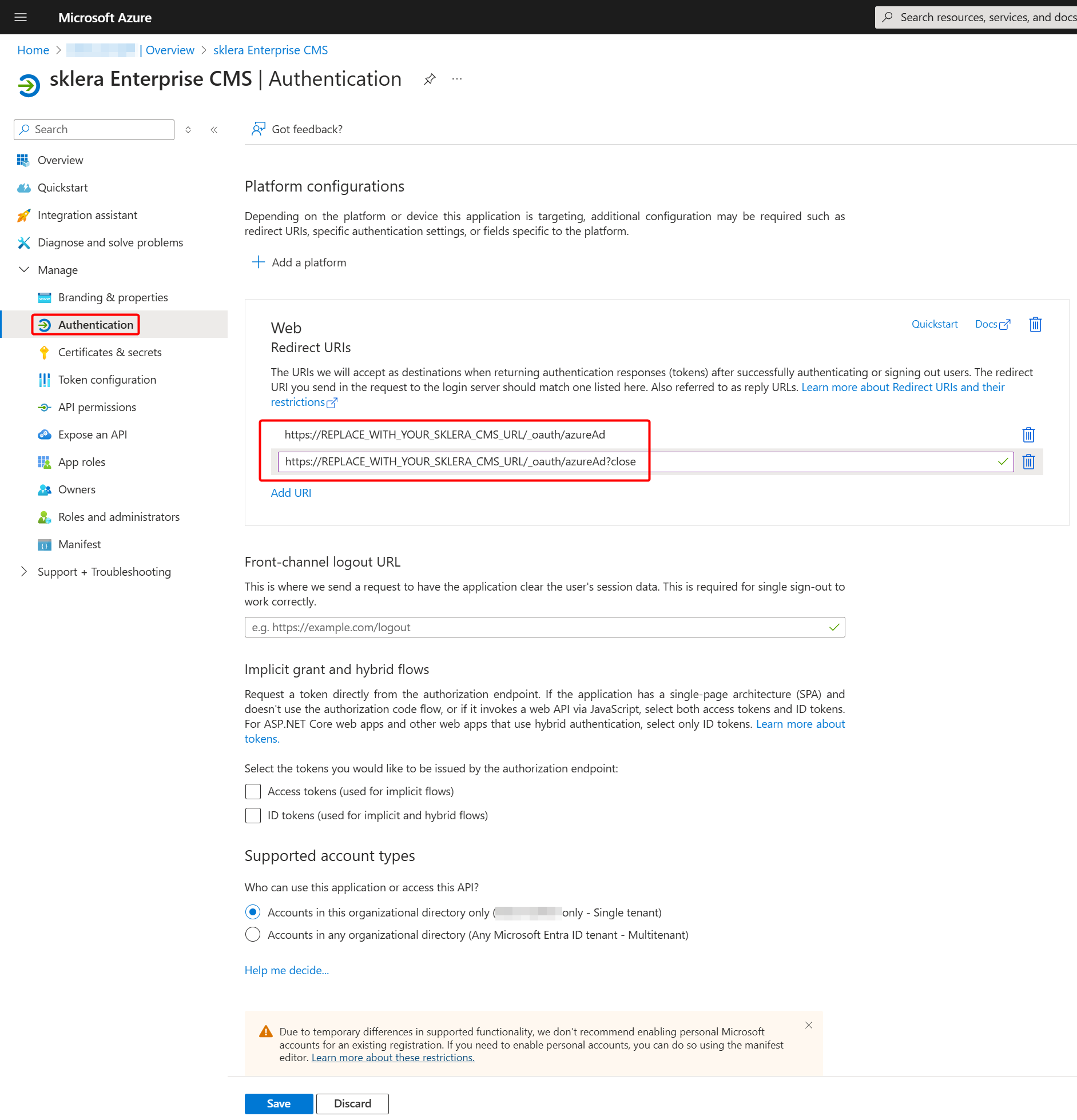
Configure Secret:

Select expiration time:

Copy client secret (value) and send it securely to sklera GmbH:

Copy Application (client) ID and Directory (tenant) ID and send it securely to sklera GmbH:

ADFS 3.0
System requirements
- Windows domain with ADFS 3.0 (Part of Windows Server 2012 R2 Enterprise or ADFS 4.0 (Part of Windows Server 2016)
- The ADFS Service needs to be accessible via https from the sklera server.
Install AD FS
Information concerning the installation and configuration of Windows AD FS can be accessed in Microsofts' TechNet Portal: https://technet.microsoft.com/en-us/library/dn452410.aspx
Configure AD FS 3.0 for sklera
The following steps are required on existing AD FS servers to add sklera as an authorized OAuth application;
- Open a Powershell console as an admin user
- Create a ADFS Client ID for the sklera application with the following command. Replace ADMIN_URL with the actual URL of your sklera server!
Add-ADFSClient -Name "sklera CMS" -ClientId "skleracms" -RedirectUri "https://ADMIN_URL/_oauth/adfsoauth" - Add a 'Relying Party Trust'. To do so open the AD FS Management tool, navigate to Trust Relationships>Relaying Party Trusts and right click on it to open the context menu. Click on 'Add Relying Party Trust'.

- Follow the instructions of the wizard. In summary:
- AD FS Profile
- Skip Encryption
- name of your own choice














- It's important to define an outgoing rule with 'id' under Claim Transformation
Activate AD FS on your sklera Server
You need to add the ADFS server in your server settings as well as the SSL certificate. To do so please get in touch with sklera GmbH via <info@sklera.tv> to do the neccessary changes.
AD Login
Once the switch has been completed you will see a new button with which you can launch an OAuth authentification.
After the first sign-on by a AD user, the user needs to be validated by an admin before he can access channels within sklera.
Hint: If you use the invitation functionality your coworker will be able to immediately access sklera.
ADFS 4.0
Steps to configure ADFS 4.0 on Windows Server 2016 to work with sklera
- Install ADFS
- Open ADFS Administration panel
- Make sure that the OAuth endpoint is active.

- Check installed certificates for validity

Export the signing certificate in CER format - this will be needed at a later stage.
Furthermore it's important that the private key for service communication can be read by the ADFS service worker. Switch to certificate administration and choose the appropriate certificate for your service account.
Warning: If you change(d) the certificate you will need to confirm this via a Powershell command - changing it in the GUI only is not enough!Set-AdfsSslCertificate -Thumbprint XXXXXX…
- Adda new Application Group for sklera by using the template "Web browser accessing a web application".

- Set the Redirect URL to https://ADMINURL/_oauth/adfsoauth (Replace ADMINURL with your sklera instance), leave the other settings unchanged. Copy the Client ID.
- Open the created application group and edit the web application. Switch to the Issuance Transform tab and add a new rule:


- Confirm with OK and restart the ADFS service.
Subsequently please transmit the Client ID and the signing certificate to sklera GmbH. These need to be added to the sklera server to complete the installation,